The European AI Act, developed after extensive legislative deliberation, is the first comprehensive regulation for artificial intelligence systems, including general-purpose AI models (GPAIMs). Given the European Union’s proactive stance on technology regulation, developers and users worldwide should closely examine the AI Act’s requirements and exceptions, particularly those related to open-source technologies. This understanding will be essential as similar regulations are likely to emerge globally in the near future.
EU AI Act: Regulation of AI Systems and GPAIMs
The AI Act aims to govern (and sometimes prohibit) the development, use, and distribution of AI systems and GPAIMs, especially where these technologies could affect life, safety, or individual legal rights. The Act underscores the inherent risks of foundational AI technologies due to their widespread adaptability and potential for pervasive use. Issues with powerful or flawed AI systems could rapidly escalate within the economy, unlike narrowly trained models with specific use cases.
Controversy and Compromise on Open-Source AI
The regulation of open-source AI technologies sparked significant debate during the legislative process. Some advocates argued that excluding exemptions for open-source models would hinder innovation and knowledge-sharing. Conversely, others highlighted security concerns associated with the unrestricted distribution of open-source models. Ultimately, the AI Act includes two key exemptions.
Overview of Open-Source Exceptions
AI Systems
The first exemption, detailed in Article 2(12), states that the AI Act does not apply to AI systems released under free and open-source licenses unless they are marketed or used as high-risk AI systems or fall under Articles 5 or 50. These articles pertain to AI systems that are prohibited or directly interact with natural persons. Determining whether an AI system falls into the prohibited or high-risk categories outlined in Articles 5 and 6, along with Annexes I and III, requires a detailed, fact-specific analysis.
General-Purpose AI Models
The AI Act also provides a limited exception for general-purpose AI models. To qualify, providers must ensure the model is accessible, usable, modifiable, and distributable, with all relevant information, such as model architecture and usage, made publicly available. However, GPAIMs presenting “systemic risks” do not qualify for this exception. These risks are defined based on the model’s high-impact capabilities or designation by the Commission.
Benefits and Requirements of the Exception
If a GPAIM meets the exception criteria, it is exempt from certain transparency obligations outlined in Article 53(1)(a) and (b), including maintaining technical documentation for downstream providers. Nevertheless, providers must share a detailed summary of the model’s training content and establish a copyright policy per EU law.
Considerations for an Open-Source AI Strategy
Inventory of AI Technologies
The first step in any AI compliance program is inventorying a business’s AI technologies. This includes proprietary, open-source, and commercially licensed AI systems and GPAIMs. Due to their rapid integration into common software services, companies often use a variety of AI models and tools, sometimes unknowingly. Hence, internal tracking and oversight are crucial for managing AI-related risks.
Licensing Compliance
Ensuring compliance with license terms, especially for third-party AI technologies, is vital to maintaining legal usage rights. Non-compliance can lead to immediate termination of licenses.
Pros and Cons for Providers
Benefits
Providers might find value in offering AI systems or GPAIMs under open-source licenses, which can stimulate innovation, enhance reputation, and attract talent. Additionally, the AI Act reduces the compliance burden for GPAIM providers by exempting them from several transparency obligations.
Drawbacks
However, the requirement to disclose details about model architecture, weights, and training could conflict with a provider’s desire to keep certain information confidential. Currently, few GPAIMs meet the open-source exception criteria, limiting available options.
Pros and Cons for Deployers
Benefits
For deployers (users), open-source AI systems and GPAIMs are cost-effective, readily accessible, and pre-developed, offering significant time and financial savings. Users also benefit from the detailed information disclosed by GPAIM providers under open-source licenses.
Drawbacks
Potential security vulnerabilities and copyleft license effects are major concerns. Users may lack assurances about open-source AI technologies’ training, suitability, and security, necessitating thorough evaluation and potential contractual obligations for providers.
Safeguards for Using Open-Source AI Technologies
Companies should implement robust operational precautions when using open-source AI technologies. This includes comprehensive internal and external testing, quality management procedures, employee policies on AI, technical documentation, log maintenance, and human oversight in AI operations. Legal and technical teams should rigorously evaluate the terms of open-source licenses to ensure they align with the company’s use cases and compliance requirements. Regular audits and tracking of license terms are essential to maintain adherence to legal obligations.
At Threatrix, we understand the complexities and challenges of navigating AI regulations like the European AI Act. Our expertise in software supply chain security and open-source license compliance ensures that your organization can leverage AI technologies confidently and securely.
Here’s how our team can help your business stay secure and compliant:
- Advanced Snippet-Level Analysis: Threatrix performs granular, snippet-level analysis, which is crucial for accurately identifying and managing compliance issues in small code segments. This level of detail allows for precisely pinpointing problematic code, even within larger, complex software projects for AI-generated and developer-written code.
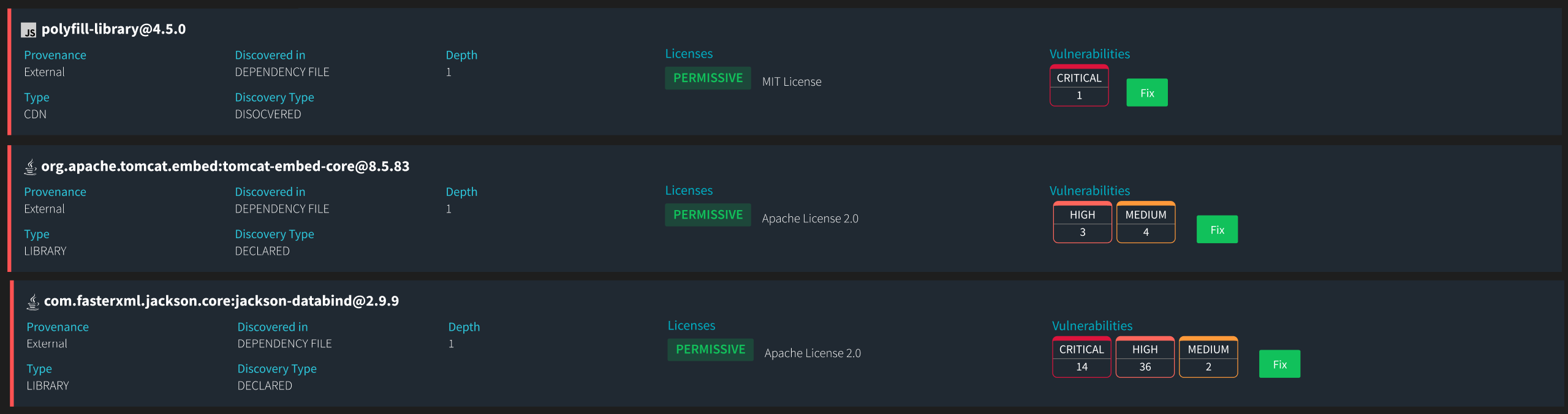
- Risk Metric Scores: Threatrix integrates risk metric scores into its analysis, quantifying each vulnerability’s potential impact. This feature helps prioritize the response efforts, ensuring that the most critical vulnerabilities, which could have the highest impact on the system’s security and compliance posture, are addressed first.
- Speed of results: Leveraging advanced AI algorithms and scalable infrastructure, Threatrix efficiently processes extensive datasets of billions of source files, enabling it to keep pace with continuous integration and deployment workflows. This high-speed analysis enhances productivity and ensures that security and compliance checks are seamlessly integrated into the development process, providing real-time insights and IDE feedback essential for maintaining stringent security standards and compliance requirements in a fast-paced development environment.
Advanced Automation
- Threatrix’s automation capabilities allow for continuous scanning and monitoring of open-source components, ensuring security and compliance without disrupting the development workflow.
- Automated remediation suggestions and policy enforcement save developers and compliance teams significant time.
- Threatrix streamlines the compliance process through automated workflows by identifying and classifying code snippets during the build phase. This proactive approach helps mitigate non-compliance risk by ensuring all open source components are properly licensed before deployment.
- Some licenses, including Apache, require the code and documentation to provide the proper attribution. Our solution simplifies the complex process of license attribution for developers. As a result of automating this process, developers can concentrate on building great software while compliance is taken care of seamlessly in the background.
- Our proof of provenance feature is crucial for managing legal risks associated with open-source software. It helps verify that all components are used in accordance with their respective licenses and have not been tampered with or altered in potentially harmful ways.
Comprehensive SBOMS
Threatrix generates detailed customizable reports, including Software Bill of Materials (SBOMs) in CycloneDX and SPDX formats and exportable license attribution reports. These reports provide clear visibility into the status of all software assets for audits and verification processes attached to every software release.
Real-Time Integration
Our solution seamlessly integrates with CI/CD pipelines and source code management (SCM) systems, enabling real-time compliance checks and vulnerability detection. It can scan billions of source files and produce scanned results in seconds.
The IDE plugin enforces customizable compliance policies within the development environment, promoting best practices from the outset. For example, suppose the compliance teams do not allow GPL licenses. In that case, the developers receive an alert in their IDE as they code that the snippet has an attached license that violates their organizational compliance policy. We then provide a side-by-side view of the copied and pasted code and suggest the percentage of code that needs to be changed.
Scalability
Designed to efficiently manage and analyze billions of source files, Threatrix scales with organizational needs, ensuring robust performance regardless of codebase size. The IDE plugin facilitates this scalability by automating compliance checks and documentation processes, thus supporting larger teams and more complex projects without adding overhead or reducing development speed.
Developer-Friendly Software Composition Analysis
The developer view dashboard provides a centralized view of vulnerability and compliance metrics, making it easy for developers to understand and act on compliance-related information.
Vulnerability remediation with Auto-Fix empowers developers to address issues promptly, reducing non-compliance risk and enhancing code security within their ID.
Languages should not be a barrier to compliance. Threatrix supports an extensive array of 420 programming languages, with new language support provided within 24 hours from developer adoption. This ensures that your compliance tools are as up-to-date as your development tools.
As software development continues to evolve, integrating robust security and compliance tools into your workflow is essential. In 2024, starting your security and compliance program with a Software Composition Analysis solution like Threatrix ensures that your codebase remains secure, compliant, and legally sound. By automating vulnerability detection and license compliance, Threatrix saves time and provides peace of mind, allowing your development team to focus on innovation and productivity.
Ready to elevate your software security and compliance strategy? Discover how Threatrix can transform your approach to managing open-source components. Schedule your demo today and join leading companies that trust Threatrix for their compliance needs.