As we continue into 2024, the importance of Software Composition Analysis (SCA) tools has reached a new peak. The best-in-class SCA solutions offer unparalleled automation that saves developers and compliance teams time and organizational costs as we enter the new realm of AI coding tools.
What is Software Composition Analysis (SCA)
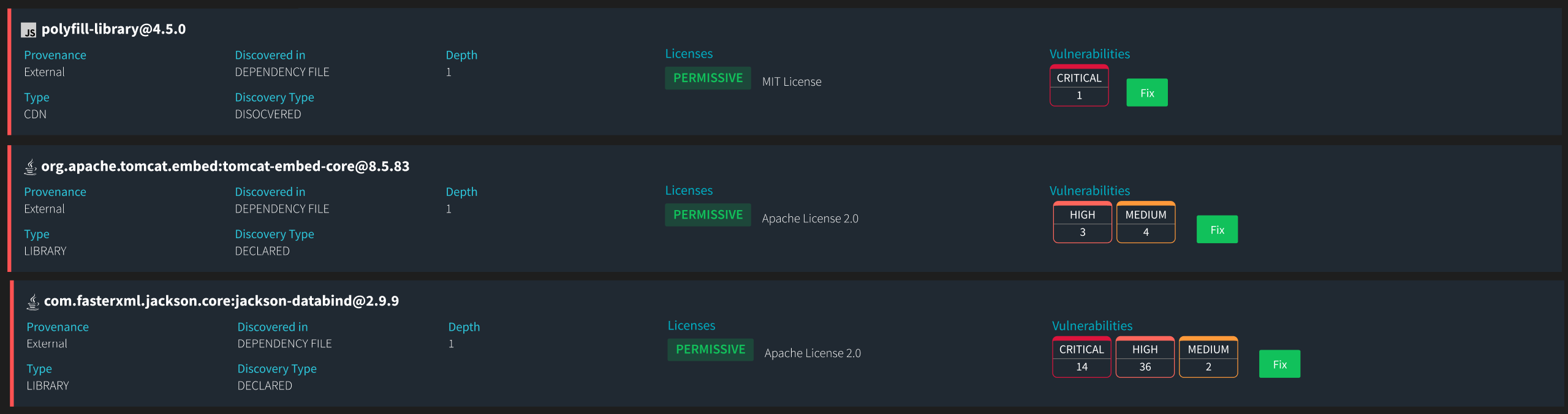
Software Composition Analysis (SCA) is a critical toolset to audit and manage open-source components within a software codebase. It allows organizations to catalog and evaluate all open-source software embedded within their applications to ensure compliance with licensing requirements and safeguard against security vulnerabilities.
By using SCA tools, companies can automate detecting outdated or vulnerable open-source libraries and ensure that any open-source licenses are compatible with their project policies. This proactive approach helps mitigate legal risks associated with license non-compliance and reduces the threat of security breaches from known vulnerabilities in open-source components. As open-source software continues to be integral to software development, implementing an effective SCA strategy becomes indispensable for maintaining the integrity and security of software products.
Why Start with SCA Over SAST and DAST in 2024
Companies should prioritize Software Composition Analysis (SCA) tools as a starting point for their security and compliance programs in 2024, particularly because a significant portion of modern software—often estimated at around 90%—comprises open-source components.
This reliance on open-source software means that the vast majority of a company’s codebase is not originally written by its own developers but rather includes dependencies and third-party libraries. Since these third-party elements can have vulnerabilities that are well-documented and targeted by attackers, using SCA tools helps companies preemptively address these risks before they can be exploited.
Now used by 95% of developers, AI coding tools are trained predominantly on vast datasets of open-source code. These AI tools, including popular coding assistants and automated programming applications, rely heavily on the diversity and breadth of open-source projects to learn various coding patterns and solutions. This reliance means that a significant portion of the code suggested or generated by AI tools can be traced back to open-source origins.
AI coding tools are designed to speed up development by automating code generation, which can lead projects to move faster into deployment phases. This rapid pace will pressure security and compliance teams to speed up the required thorough checks and balances to ensure the software is secure and compliant. The speed of development can outpace these teams’ ability to address all potential issues adequately. Security and compliance teams must scale their efforts accordingly, often requiring advanced tools and more sophisticated strategies to manage the sheer volume of code effectively.
While AI coding tools bring undeniable benefits in terms of efficiency and productivity, they also require organizations to adapt their security and compliance frameworks to manage the new risks these tools introduce.
Early Detection of Open Source Vulnerabilities
- SCA: Identifies known vulnerabilities in open-source components early in the development lifecycle, mitigating risks before deployment.
- SAST (Static Application Security Testing): Focuses on identifying vulnerabilities in proprietary code during the coding phase.
- DAST (Dynamic Application Security Testing): Detects vulnerabilities in running applications during the testing phase.
Comprehensive Security and Compliance Coverage
- SCA tools analyze dependencies and third-party libraries, ensuring all components are secure and compliant.
- SAST and DAST tools focus on the code developers write, missing vulnerabilities in external libraries.
Open Souce License Compliance
- SCA tools track and manage open-source licenses, helping companies avoid legal issues from improper use of open-source software.
- SAST and DAST tools do not address open source license compliance.
While SAST and DAST are important for a comprehensive security strategy, they do not provide the same level of scrutiny for external libraries and dependencies as SCA tools. Starting with SCA ensures that the larger, often more vulnerable portion of the codebase, which includes these external elements, is secured and compliant, forming a strong foundation for further security measures.
Efficiency and Automation
The best-in-class Software Composition Analysis (SCA) tools not only automate the detection and management of vulnerabilities and license compliance down to the snippet level but also integrate risk metric scores, significantly reducing manual effort for developers and compliance teams. These scores help prioritize vulnerabilities based on their potential impact, allowing teams to address the most critical issues first. This streamlined approach enhances efficiency and ensures that resources are allocated effectively, focusing on mitigating the highest risks to the software’s security and compliance posture.
Organizations must equip themselves with advanced software composition analysis tools that offer rapid scanning capabilities to manage the risks associated with AI-generated code effectively. The tool should be able to scan billions of source files and deliver results in seconds during the build process. Such tools should be capable of quickly scanning entire codebases, allowing security and compliance teams to keep up with the fast pace of AI-driven development.
Additionally, integrating an IDE plugin that can detect risks at the earliest stages of coding—shifting security to the left—is crucial. This setup ensures that potential issues are identified and addressed as early as possible in the development process, significantly reducing the chances of vulnerabilities making it to production. These features are essential for organizations looking to mitigate the security and compliance challenges posed by the increasing use of AI in software development.
Threatrix: The Best in Class Software Composition Analysis Tool
Advanced Capabilities
- Advanced Snippet-Level Analysis: Threatrix performs granular, snippet-level analysis, which is crucial for accurately identifying and managing compliance issues in small code segments. This level of detail allows for precisely pinpointing problematic code, even within larger, complex software projects for AI-generated and developer-written code.
- Risk Metric Scores: Threatrix integrates risk metric scores into its analysis, quantifying each vulnerability’s potential impact. This feature helps prioritize the response efforts, ensuring that the most critical vulnerabilities, which could have the highest impact on the system’s security and compliance posture, are addressed first.
- Speed of results: Leveraging advanced AI algorithms and scalable infrastructure, Threatrix efficiently processes extensive datasets of billions of source files, enabling it to keep pace with continuous integration and deployment workflows. This high-speed analysis enhances productivity and ensures that security and compliance checks are seamlessly integrated into the development process, providing real-time insights and IDE feedback essential for maintaining stringent security standards and compliance requirements in a fast-paced development environment.
Advanced Automation
- Threatrix’s automation capabilities allow for continuous scanning and monitoring of open-source components, ensuring security and compliance without disrupting the development workflow.
- Automated remediation suggestions and policy enforcement save developers and compliance teams significant time.
- Threatrix streamlines the compliance process through automated workflows by identifying and classifying code snippets during the build phase. This proactive approach helps mitigate non-compliance risk by ensuring all open source components are properly licensed before deployment.
- Some licenses, including Apache, require the code and documentation to provide the proper attribution. Our solution simplifies the complex process of license attribution for developers. As a result of automating this process, developers can concentrate on building great software while compliance is taken care of seamlessly in the background.
- Our proof of provenance feature is crucial for managing legal risks associated with open-source software. It helps verify that all components are used in accordance with their respective licenses and have not been tampered with or altered in potentially harmful ways.
Comprehensive SBOMS
Threatrix generates detailed customizable reports, including Software Bill of Materials (SBOMs) in CycloneDX and SPDX formats and exportable license attribution reports. These reports provide clear visibility into the status of all software assets for audits and verification processes attached to every software release.
Real-Time Integration
Our solution seamlessly integrates with CI/CD pipelines and source code management (SCM) systems, enabling real-time compliance checks and vulnerability detection. It can scan billions of source files and produce scanned results in seconds.
The IDE plugin enforces customizable compliance policies within the development environment, promoting best practices from the outset. For example, suppose the compliance teams do not allow GPL licenses. In that case, the developers receive an alert in their IDE as they code that the snippet has an attached license that violates their organizational compliance policy. We then provide a side-by-side view of the copied and pasted code and suggest the percentage of code that needs to be changed.
Scalability
Designed to efficiently manage and analyze billions of source files, Threatrix scales with organizational needs, ensuring robust performance regardless of codebase size. The IDE plugin facilitates this scalability by automating compliance checks and documentation processes, thus supporting larger teams and more complex projects without adding overhead or reducing development speed.
Developer-Friendly Software Composition Analysis
The developer view dashboard provides a centralized view of vulnerability and compliance metrics, making it easy for developers to understand and act on compliance-related information.
Vulnerability remediation with Auto-Fix empowers developers to address issues promptly, reducing non-compliance risk and enhancing code security within their ID.
Languages should not be a barrier to compliance. Threatrix supports an extensive array of 420 programming languages, with new language support provided within 24 hours from developer adoption. This ensures that your compliance tools are as up-to-date as your development tools.
As software development continues to evolve, integrating robust security and compliance tools into your workflow is essential. In 2024, starting your security and compliance program with a Software Composition Analysis solution like Threatrix ensures that your codebase remains secure, compliant, and legally sound. By automating vulnerability detection and license compliance, Threatrix saves time and provides peace of mind, allowing your development team to focus on innovation and productivity.
Ready to elevate your software security and compliance strategy? Discover how Threatrix can transform your approach to managing open-source components. Schedule your demo today and join leading companies that trust Threatrix for their compliance needs.